Threat Intelligence Blog

Contact us to discuss any insights from our Blog, and how we can support you in a tailored threat intelligence report.
Cyber Briefing 23 October 2020: Ransomware Continues to Evolve; Infected IoT Up 100%; Brute Force Attacks Up with more Open RDP Ports; 40% Unsure on Mobile Phishing; Most Imitated Phishing Brands
Cyber Briefing 23 October 2020: Ransomware Variants Evolve as Crooks Chase Bigger Paydays; Infected IoT Surges 100% in a Year; Brute Force Attacks Up Due To More Open RDP Ports; 40% of Users Not Sure What Mobile Phishing Is; Microsoft Most Imitated Phishing Brand Q3 2020; DDoS Triples as Ransoms Re-Emerge; Exploited Chrome Bug Fixed; WordPress Forces Security Update; The Most Worrying Vulns Around Today
Welcome to this week’s Black Arrow Cyber Threat Briefing – a weekly digest, collated and curated by our cyber experts to provide senior and middle management with an easy to digest round up of the most notable threats, vulnerabilities and cyber related news from the last week.
Threats
Ransomware
This week has been busy with ransomware related news, including new charges against Russian state-sponsored hackers and numerous attacks against well-known organisations.
In 2017, there was an attack utilizing the NotPetya ransomware to destroy data on systems worldwide. This week, the US govt indicted six Russian intelligence operatives [source], known to be part of the notorious 'Sandworm' group, for hacking operations, including NotPetya.
Ransomware variants continue to evolve as crooks chase bigger paydays
The number of ransomware attacks which threaten to leak stolen data if the victim doesn't pay a ransom to get their encrypted files and servers back is growing – and this is being reflected in the changing nature of the cyber criminal market.
Analysis by cyber security researchers found that over the last three months – between July and September - 80 percent of ransomware attacks combined with data dumps were associated with four families of ransomware – Maze, Sodinokibi, Conti and Netwalker.
The period from April to June saw just three ransomware families account for 80 percent of alerts – DoppelPaymer, Maze and Sodinokibi.
The way DoppelPayer has dropped off and how Conti and NetWalker have suddenly emerged some of the most prolific threats shows how the ransomware space continues to evolve, partly because of how successful it has already become for the crooks behind it. [source]
Why this matters:
Maze was the first major family of ransomware to add threats of data breaches to their ransom demands and other ransomware operators have taken note – and stolen the additional extortion tactic.
There is an inherent competitive nature that has befallen the ransomware landscape. The saturated ransomware market pushes ransomware developers to cut through the noise and gain the best ransomware title and this drives more affiliates to carry out their work and, thus, more successful attacks to reach their goal: to make as much money as possible.
DoppelPaymer's activity has dropped over the last few months – although it still remains active - enabling Conti and NetWalker to grab a larger slice of the pie.
Notable ransomware victims of the last week
French IT giant Sopra Steria hit by Ryuk ransomware
French IT services giant Sopra Steria suffered a cyber attack on October 20th, 2020, that reportedly encrypted portions of their network with the Ryuk ransomware.
Sopra Steria is a European information technology company with 46,000 employees in 25 countries worldwide. The company provides a wide range of IT services, including consulting, systems integration, and software development.
The firm has said that the attack has hit all geographies where they operate and have said it will take them several weeks to recover.
Numerous sources have confirmed that it was Ryuk ransomware threat actors who were behind the attack. This hacking group is known for its TrickBot and BazarLoader infections that allow threat actors to access a compromised network and deploy the Ryuk or Conti ransomware infections.
BazarLoader is increasingly being used in Ryuk attacks against high-value targets due to its stealthy nature and is less detected than TrickBot by security software.
When installed, BazarLoader will allow threat actors to remotely access the victim's computer and use it to compromise the rest of the network.
After gaining access to a Windows domain controller, the attackers then deploy the Ryuk ransomware on the network to encrypt all of its devices, as illustrated in the diagram above. [Source1] [source2]
The Nefilim ransomware operators have posted a long list of files that appear to belong to Italian eyewear and eyecare giant Luxottica.
Luxottica Group S.p.A. is an Italian eyewear conglomerate and the world’s largest company in the eyewear industry (which owns brands including LensCrafters, Sunglass Hut, Apex by Sunglass Hut, Pearle Vision, Target Optical, Eyemed vision care plan, and Glasses.com. Its best known brands are Ray-Ban, Persol, and Oakley) and employs over 80,000 people and generated 9.4 billion in revenue for 2019.
The company was hit by a cyber attack and some of the web sites operated by the company were not reachable, including Ray-Ban, Sunglass Hut, LensCrafters, EyeMed, and Pearle Vision.
Reports indicate that the firm was using a Citrix ADX controller device vulnerable to a critical vulnerability and it is believed that a threat actor or actors exploited the above flaw to infect the systems at the company with ransomware. This appears to have subsequently confirmed with Nefilim ransomware operators having posted a long list of files that appear to belong to Luxottica. [source]
Why this matters:
The analysis of the leaked files revealed that they contain confidential information regarding the recruitment process, professional resumes, and info about the internal structures of the Group’s human resource department. The ransomware operators also published a message which accuses Luxottica of having failed the properly manage the attack.
In the past months, the number of ransomware attacks surged, numerous ransomware gangs made the headlines targeting organisations worldwide and threatening victims with releasing the stolen data if the ransom was not paid.
Extortion is the new thing in cyber crime right now, more so than in the past. Companies cannot hide the cyber attack anymore. Now it’s more about how to manage the breach from the communication perspective. Defending companies from these types of attacks becomes even more strategic: data leak damages can generate tremendous amount of costs for companies worldwide.
Other notable ransomware victims this week include:
Barnes & Noble hit by Egregor ransomware, strange data leaked [source]
Montreal's STM public transport system hit by ransomware attack [source]
WastedLocker ransomware hits US-based ski and golf resort operator Boyne Resorts (WastedLocker was the same one used in the attack on Garmin in July) [source]
Other Threats
Infected IoT Device Numbers Surge 100% in a Year
The volume of infected Internet of Things (IoT) devices globally has soared by 100% over the past year, according to new data from Nokia.
It revealed that infected IoT devices now comprise nearly a third (32.7%) of the total number of devices, up from 16.2% in the 2019 report.
Nokia argued that infection rates for connected devices depend dramatically upon the visibility of the devices on the internet.
In networks where devices are routinely assigned public facing internet IP addresses there is a higher infection rate. In networks where carrier grade NAT is used, the infection rate is considerably reduced, because the vulnerable devices are not visible to network scanning.
With the introduction of 5G well underway, it is expected that not only the number of IoT devices will increase dramatically, but also the share of IoT devices accessible directly from the internet will increase as well, and rates of infection rising accordingly. [source]
Brute force attacks increase due to more open RDP ports
While leaving your back door open while you are working from home may be something you do without giving it a second thought, having unnecessary ports open on your computer or on your corporate network is a security risk that is sometimes underestimated. That’s because an open port can be subject to brute force attacks.
A brute force attack is where an attacker tries every way he can think of to get in. Including throwing the kitchen sink at it. In cases where the method they are trying is to get logged in to your system, they will try endless combinations of usernames and passwords until a combination works.
Brute force attacks are usually automated, so it doesn’t cost the attacker a lot of time or energy. Certainly not as much as individually trying to figure out how to access a remote system. Based on a port number or another system specific property, the attacker picks the target and the method and then sets his brute force application in motion. He can then move on to the next target and will get notified when one of the systems has swallowed the hook.
RDP attacks are one of the main entry points when it comes to targeted ransomware operations. To increase effectiveness, ransomware attacks are getting more targeted and one of the primary attack vectors is the Remote Desktop Protocol (RDP). Remote desktop is exactly what the name implies, an option to remotely control a computer system. It almost feels as if you were actually sitting behind that computer. Which is exactly what makes an attacker with RDP access so dangerous. [source]
Why this matters:
Because of the current pandemic, many people are working from home and may be doing so for a while to come. Working from home has the side effect of more RDP ports being opened. Not only to enable the workforce to access company resources from home, but also to enable IT staff to troubleshoot problems on the workers’ devices. A lot of enterprises rely on tech support teams using RDP to troubleshoot problems on employee’s systems.
But ransomware, although prevalent, is not the only reason for these types of attacks. Cyber criminals can also install keyloggers or other spyware on target systems to learn more about the organization they have breached. Other possible objectives might be data theft, espionage, or extortion.
Phishing
Two in five employees are not sure what a mobile phishing attack is
The COVID-19 pandemic has clearly changed the way people work and accelerated the already growing remote work trend. This has also created new security challenges for IT departments, as employees increasingly use their own personal devices to access corporate data and services.
These changes, where employees, IT infrastructures, and customers are everywhere – has led to employees not prioritising security in their new world of work, and the current distributed remote work environment has also triggered a new threat landscape, with malicious actors increasingly targeting mobile devices with phishing attacks.
A new study looking at the impact that lockdown has had on employees working habits polled 1,200 workers across the US, UK, France, Germany, Belgium, Netherlands, Australia, and New Zealand showed that many employees were unaware of how to identify and avoid a phishing attack, and over two in five (43%) of employees are not even sure what a phishing attack is. [source]
Microsoft is Most Imitated Brand for Phishing Attempts in Q3 2020
The latest Check Point ‘Q3 Brand Phishing Report’, highlighting the brands that hackers imitated the most to lure people into giving up personal data, reveals the brands which were most frequently imitated by criminals in their attempts to steal individuals’ personal information or payment credentials during July, August and September.
In Q3, Microsoft was the most frequently targeted brand by cyber criminals, soaring from fifth place (relating to 7% of all brand phishing attempted globally in Q2 of 2020) to the top of the ranking. 19% of all brand phishing attempts related to the technology giant, as threat actors sought to capitalise on large numbers of employees still working remotely during the Covid-19 pandemic. For the first time in 2020, DHL entered the top 10 rankings, taking the second spot with 9% of all phishing attempts related to the company. [source]
Top phishing brands in Q3 2020
Microsoft (19%)
DHL (9%)
Google (9%)
PayPal (6%)
Netflix (6%)
Facebook (5%)
Apple (5%)
Whatsapp (5%)
Amazon (4%)
Instagram (4%)
Phishing Lures Shifting from COVID-19 updates to Job Opportunities
Researchers are seeing a pivot in the spear-phishing and phishing lures used by cybercriminals, to entice potential job candidates as businesses start to open up following the pandemic.
Cyber criminals cashed in on the surge of COVID-19 earlier this year, with email lures purporting to be from healthcare professionals offering more information about the pandemic. However, as the year moves forward, bad actors are continuing to swap up their attacks and researchers are now seeing ongoing email based attacks that tap into new job opportunities as businesses start to open up. [source]
Denial of Service Attacks
DDoS (Distributed Denial of Service) Attacks Triple in Size as Ransom Demands Re-Emerge
The last quarter of 2020 has seen a wave of web application attacks which have used ransom letters to target businesses across a number of industries.
According to research from Akamai, the largest of these attacks sent over 200Gbps of traffic at their targets as part of a sustained campaign of higher Bits Per Second (BPS) and Packets Per Second (PPS) than similar attacks had displayed a few weeks prior.
Prior to August most of these attacks were targeting the gaming industry but since then these attacks abruptly swung to financial organisations, and later in the cycle, multiple other verticals.
Akamai explained that none of the vectors involved in these series of attacks were new, as most of the traffic was generated by reflectors and systems that were used to amplify traffic. However, multiple organisations began to receive targeted emails with threats of DDoS attacks, where this would be launched unless a ransom amount was paid. A small DDoS would be made against the company to show that the attackers were serious, and then there was a threat of a 1Tbps attack if payment was not made.
Many extortion DDoS campaigns start as a threat letter, and never progress beyond that point but this this campaign has seen frequent ‘sample’ attacks that prove to the target that criminals have the capability to make life difficult.
Many of the extortion emails ended up being caught by spam filters, and not all targets are willing to admit they’ve received an email from the attackers.
Why this matters:
This extortion DDoS campaign is not over and the criminals behind this campaign are changing and evolving their attacks in order to throw off defenders and the law enforcement agencies that are working to track them down.
Vulnerabilities
New Google Chrome version fixes actively exploited zero-day bug
Google released Chrome 86.0.4240.111 this week to address five security vulnerabilities, one of which is being actively exploited.
The announcement from Google stated they they were aware of reports that an exploit for CVE-2020-15999 exists in the wild.
This new version of Chrome started rolling out to the entire userbase. Users on Windows, Mac, and Linux desktop users can upgrade to Chrome 86 by going to Settings -> Help -> About Google Chrome.
The Google Chrome web browser will then automatically check for the new update and install it when available.
Adobe releases another out-of-band patch, squashing critical bugs across creative software
Adobe has released a second out-of-band security update to patch critical vulnerabilities across numerous software products.
The patch, released outside of the tech giant's typical monthly security cycle, impacts Adobe Illustrator, Dreamweaver, Marketo, Animate, After Effects, Photoshop, Premiere Pro, Media Encoder, InDesign, and the Creative Cloud desktop application on Windows and macOS machines.
The vulnerabilities across the different products variously could result in privilege escalation, cross-site scripting (XSS), which could be weaponised to deploy malicious JavaScript in a browser session, or otherwise could result in arbitrary code execution.
Last week, Adobe released a separate set of out-of-band security fixes impacting the Magento platform. On October 15, Adobe said the patch resolved nine vulnerabilities, eight of which are critical -- including a bug that could be abused to tamper with Magento customer lists. [source]
WordPress deploys forced security update for dangerous bug in popular plugin
The WordPress security team has taken a rare step last week and used a lesser-known internal capability to forcibly push a security update for a popular plugin called Loginizer, which provides security enhancements for the WordPress login page, but that was found to contain a dangerous SQL injection bug that could have allowed hackers to take over WordPress sites running older versions of the plugin. [source]
Why this matters:
Remote attackers to run code against the WordPress database — in what is referred to as an unauthenticated SQL injection attack.
These are the most worrying vulnerabilities around today
Failure to patch once again leaves organisations open to attacks
The US National Security Agency (NSA) has published a new cyber security advisory in which it details 25 of the most dangerous vulnerabilities actively being exploited in the wild by Chinese state-sponsored hackers and other cyber criminals.
Unlike zero-day vulnerabilities where hardware and software makers have yet to release a patch, all of the vulnerabilities in the NSA's advisory are well-known and patches have been made available to download from their vendors. However, the problem lies in the fact that organisations have yet to patch their systems, leaving them vulnerable to potential exploits and attacks.
The NSA provided further details on the nature of the vulnerabilities in its advisory while urging organisations to patch them immediately.
Most of the vulnerabilities listed below can be exploited to gain initial access to victim networks using products that are directly accessible from the Internet and act as gateways to internal networks. The majority of the products are either for remote access or for external web services and should be prioritised for immediate patching. The full list can be found here.
The first bug in the list, tracked as CVE-2019-11510, relates to Pulse Secure VPN servers and how an unauthenticated remote attacker can expose keys or passwords by sending a specially crafted URI to perform an arbitrary file reading vulnerability.
Another notable bug from the list, tracked as CVE-2020-5902, affects the Traffic Management User Interface (TMUI) of F5 BIG-IP proxies and load balancers and it is vulnerable to a Remote Code Execution (RCE) vulnerability that if exploited, could allow a remote attacker to take over an entire BIG-IP device.
The Citrix Application Delivery Controller (ADC) and Gateway systems are vulnerable to a directory traversal bug, tracked as CVE-2019-19781, that can lead to remote code execution where an attacker does not need to possess valid credentials for the device.
The advisory also mentions BlueKeep, SigRed, Netlogon, CurveBall and other more well-known vulnerabilities.
To avoid falling victim to any potential attacks exploiting these vulnerabilities, the NSA recommends that organisations keep their systems and products updated and patched as soon as possible after vendors release them. [source]
Miscellaneous Cyber News of the Weeks
Hackers Can Clone Millions of Toyota, Hyundai, and Kia Keys
Owners of cars with keyless start systems have learned to worry about so-called relay attacks, in which hackers exploit radio-enabled keys to steal vehicles without leaving a trace. Now it turns out that many millions of other cars that use chip-enabled mechanical keys are also vulnerable to high-tech theft. A few cryptographic flaws combined with a little old-fashioned hot-wiring—or even a well-placed screwdriver—lets hackers clone those keys and drive away in seconds.
Researchers this week revealed new vulnerabilities in the encryption systems used by immobilisers, the radio-enabled devices inside of cars that communicate at close range with a key fob to unlock the car's ignition and allow it to start. Specifically, they found problems in how Toyota, Hyundai, and Kia implement their encryption system. A hacker who swipes a relatively inexpensive RFID reader/transmitter device near the key fob of any affected car can gain enough information to derive its secret cryptographic value. That, in turn, would allow the attacker to spoof the device to impersonate the key inside the car, disabling the immobiliser and letting them start the engine.
The researchers say the affected car models include the Toyota Camry, Corolla, and RAV4; the Kia Optima, Soul, and Rio; and the Hyundai I10, I20, and I40, amongst others. [source]
As usual, contact us to help assess where your risks lie and to ensure you are doing all you can do to keep you and your business secure.
Look out for our weekly ‘Cyber Tip Tuesday’ video blog and on our YouTube channel.
You can also follow us on Facebook, Twitter and LinkedIn.
Links to articles are for interest and awareness and linking to or reposting external content does not endorse any service or product, likewise we are not responsible for the security of external links.
Cyber Threat Briefing 16 October 2020: ransomware tidal wave; notable ransomware victims from the last week; BEC Attacks: Nigeria no longer epicentre, losses top $26B; Trickbot back; MS fix 87 vulns
Cyber Threat Briefing 16 October 2020: ransomware tidal wave of attacks; Notable ransomware victims of the last week; BEC Attacks: Nigeria No Longer the Epicentre as Losses top $26B; Trickbot back after disruption attempts; Microsoft October 2020 Patch Tuesday fixes 87 vulnerabilities; Malware gangs love open source offensive hacking tools
Welcome to this week’s Black Arrow Cyber Threat Briefing – a weekly digest, collated and curated by our cyber experts to provide senior and middle management with an easy to digest round up of the most notable threats, vulnerabilities and cyber related news from the last week.
Threats
Ransomware
Ransomware is growing and growing and getting worse all the time, with the G7 this week warning of ‘a tidal wave of ransomware attacks’ [source]. It is fast approaching becoming such a problem that it may soon reach epidemic status with few organisations left unaffected as firm after firm falls victim.
The ransomware gangs have turned crime into a multi-million pound business empire, it is estimated that $7.5 billion was extorted from victims last year in the United States alone [source], putting any legitimate industry or business sector to shame in term of meteoric growth. This is not small scale actors working out of their bedrooms, they have customer support centres and 24/7 helplines, they have plush offices and flash cars, paid for by the victims of their crimes, paid for by firms like yours paying ransoms.
And here's how attackers are getting in: in nearly half (47%) of ransomware cases gangs used the open remote desktop protocol, a tool that has been used by many companies to help staff work from home, but which can also give attackers a way in if it is not correctly secured.
More than a quarter (26%) of cases were traced back to a phishing email, and a smaller number used specific vulnerability exploits (17%), including Citrix NetScaler CVE-2019-19781 and Pulse VPN CVE-2019-11510. This was followed by account takeovers, at 10%. [source]
Criminal gangs have earned so much money and power they are now outsourcing much of the labour, allowing them to live of their spoils while their empires continue to grow, while they do next to nothing, with more and more joining their ranks [source]
As long as even a small number of victims pay the ransom this remains highly lucrative for attackers.
The ransom for Software AG is $23m, but they will demand much smaller sums from much smaller firms – so how are they doing this? Are larger firms being specifically targeted with tailored phishing campaigns, where they hope they will get lucky in getting an employee to fall for the bait, where lower value targets are being hit with machine/algorithmic generated phishing attacks, with lower levels of sophistication and more of a ‘spray and pray’ approach, hoping casting a wide enough net will still result in larger numbers of lower value victims.
We keep trying to warn firms how bad this is getting, and we don’t do this to drum up business, we do this because we are hugely concerned about the direction this is going and how damaging this can be for any firm.
Many firms are reluctant to take cyber security seriously, believing it won’t happen to them, but it is happening to firm after firm after firm who believed it wouldn’t happen to them. It’s too late to start thinking about what you should have done after you’ve become a victim, it’s far better, and far cheaper, to take steps to avoid being a victim in the first place than trying to recover or pay the ransom.
Of the increasing number of firms that do go hit, many don’t survive, and those that do often find things are never the same again, with impacts on confidence levels in your staff and in your IT and information security departments [source]
Ransomware is not only affecting desktops, laptops and servers, but also now increasingly Android and other mobile platforms [source]
Protecting against ransomware is not a luxury or something that can kicked down the road to look at another day, firms need to ensure they are protecting themselves against this threat now – before they become a victim.
Notable ransomware victims of the last week
There have been a number of high profile victims of ransomware in the last week, notably Software AG, a German conglomerate with operations in more than 70 countries, which was attacked by the Clop group who are threatening to dump stolen data if the $23 million ransom is not paid.
Carnival Cruises were hit with ransomware affecting data and personal information for guests, employees and crew for Carnival Cruises, Holland America and Seabourn as well as casino operations.
Early indications point to the disruption being experiences by Hackney Council with their systems stemming from a ransomware attack, although this has not been confirmed.
BEC
BEC Attacks: Nigeria No Longer the Epicentre as Losses top $26B
Business Email Compromise (BEC) Fraudsters now have bases of operation across at least 39 countries and are responsible for $26 billion in losses annually, and growing.
A study of more than 9,000 instances of BEC attacks all over the world shows that the number has skyrocketed over the past year, and that the social-engineering scam has expanded well beyond its historic roots in Nigeria.
Why this matters:
A recent report entitled The Global Reach of Business Email Compromise, found that these attacks cost businesses a staggering $26 billion every year. And that trend appears to be accelerating. In fact, researchers found BEC attacks currently make up a full 40 percent of cyber crime losses globally, impacting at least 177 countries.
For context, the Anti-Phishing Working Group recently find that the average wire transfer in a BEC scan is around $80,000.
In a BEC attack, a scammer impersonates a company executive or other trusted party and tries to trick an employee responsible for payments or other financial transactions into writing money to a bogus account. Attackers usually conduct a fair amount of recon work, studying executive styles and uncovering the organisations vendors, billing system practices and other information to help mount a convincing attack.
Read more: https://threatpost.com/bec-attacks-nigeria-losses-snowball/160118/
Trickbot back after disruption attempts
The Trickbot botnet looks to be working once again, despite separate efforts in the past few weeks aimed at disrupting its operation.
Earlier this month the Emotet spam botnet – which is often the precursor to TrickBot being loaded onto a system – began receiving spam templates intended for mass distribution. These spam templates contained Microsoft Word document attachments with malicious macros that fetch and load a copy of Emotet onto the victim machine. The Emotet bot reached out to its controllers and received commands to download and execute Trickbot on victim machines.
The Trickbot group tag that researchers identified is tied to a typical infection campaign that information security researchers have been observing for the past 6 months or more.
Additionally, Intel 471 researchers saw an update to the Trickbot plugin server configuration file. Fifteen server addresses were added, and two old servers were retained in the configuration, along with the server’s ‘.onion’ address. This was likely done as a fix that would help operators maintain that their infrastructure remains operational. [link]
Why this matters:
The fix is another round in the back-and-forth between Trickbot’s operators and the separate public and private sector parties that have attempted to disrupt the botnet’s actions. This includes actions by the US Cyber Command and Microsoft, who issued a public statement that it had taken legal action to “combat ransomware ahead of U.S. elections.” The legal action involved Microsoft attempting to disrupt a number of Trickbot command and control server IP addresses in the United States.
The fact that Trickbot has resumed normal operations despite the best efforts of the likes of the US Cyber Command and Microsoft shows how resilient of an operation Trickbot is, and how much more effort is needed to fully take the botnet offline for good. The botnet’s operators have all the IT support of legitimate enterprises – continuity planning, backups, automated deployment, and a dedicated workforce – that allow them to quickly react to disruptive measures.
Read more: https://public.intel471.com/blog/trickbot-online-emotet-microsoft-cyber-command-disruption-attempts/
Vulnerabilities
Microsoft October 2020 Patch Tuesday fixes 87 vulnerabilities
Microsoft this week released its monthly batch of security updates known as Patch Tuesday, and this month the OS maker has patched 87 vulnerabilities across a wide range Microsoft products.
By far, the most dangerous bug patched this month is CVE-2020-16898. Described as a remote code execution (RCE) vulnerability in the Windows TCP/IP stack, this bug can allow attackers to take over Windows systems by sending malicious ICMPv6 Router Advertisement packets to an unpatched computer via a network connection.
Another bug to keep an eye on is CVE-2020-16947, a remote code execution issue in Outlook. Microsoft says this bug can be exploited by tricking a user to open a specially crafted file with an affected version of Microsoft Outlook software. [source1] [source2]
Why this matters:
The bug was discovered internally by Microsoft engineers, and OS versions vulnerable to CVE-2020-16898 include Windows 10 and Windows Server 2019.
With a severity score of 9.8 out of a maximum 10, Microsoft considers the bug dangerous and likely to be weaponised, and rightfully so.
Patching the bug is recommended, but workarounds such as disabling ICMPv6 RDNSS support also exist, which would allow system administrators to deploy temporary mitigations until they quality-test this month’s security updates for any OS-crashing bugs.
Critical SonicWall VPN Portal Bug Allows DoS, Worming RCE
A critical security bug in the SonicWall VPN Portal can be used to crash the device and prevent users from connecting to corporate resources. It could also open the door to remote code execution (RCE), researchers said.
The flaw (CVE-2020-5135) is a stack-based buffer overflow in the SonicWall Network Security Applicance (NSA). According to researchers who discovered it, the flaw exists within HTTP/HTTPS service used for product management and SSL VPN remote access. [source]
Why this matters:
An unskilled attacker could trigger a persistent denial-of-service condition using an unauthenticated HTTP request involving a custom protocol handler.
Adding insult to injury, this particular flaw exists in a pre-authentication routine, and within a component (SSL VPN) which is typically exposed to the public internet.
‘More Than A Billion’ Phone Wide Open To ‘Backdoor’ Remote Code Execution in Adtech Company’s Code
Malicious code impacting more than a billion smartphone owners is currently in the wild and enabling remote code execution. [source]
Why this matters:
Remote code execution is a very serious security violation, and basically enables the owner of that code do almost anything they want on your phone.
Miscellaneous Cyber News of the Weeks
Malware gangs love open source offensive hacking tools
In the cyber security field, the term OST (Open Source Tools) refers to software apps, libraries, and exploits that possess offensive hacking capabilities and have been released as either free downloads or under an open source license.
OST projects are usually released to provide a proof-of-concept exploit for a new vulnerability, to demonstrate a new (or old) hacking technique, or as penetration testing utilities shared with the community.
These discussions have been taking place for more than a decade. However, they have always been based on personal experiences and convictions, and never on actual raw data.
That changed this week when a security researcher compiled data on 129 open source offensive hacking tools and searched through malware samples and cyber-security reports to discover how widespread was the adoption of OST projects among hacking groups — such as low-level malware gangs, elite financial crime groups, and even nation-state sponsored APTs. [source]
The results were compiled in an interactive map – available here
Why this matters:
Today, OST is one of the most (if not the most) controversial topics in the information security community.
On one side, you have the people who are in favour of releasing such tools, arguing that they can help defenders learn and prepare systems and networks for future attacks.
On the opposing side, you have the ones who say that OST projects help attackers reduce the costs of developing their own tools and hiding activities into a cloud of tests and legitimate pen-tests.
Fitbit Spyware Steals Personal Data via Watch Face
A researcher has found they can take advantage of lax Fitbit privacy controls to build a malicious spyware watch face.
A wide-open app-building API (Application Programming Interface) could allow an attacker to build a malicious application that could access Fitbit user data, and send it to any server.
A proof-of-concept was created to do just that, after realizing that Fitbit devices are loaded with sensitive personal data. [source]
Why this matters:
Essentially, the API could send device type, location and user information including gender, age, height, heart rate and weight and it could also access calendar information. While this doesn’t include PII profile data, the calendar invites could expose additional information such as names and locations.
The researcher was able to make the app available through the Fitbit Gallery (where Fitbit showcases various third-party and in-house apps). Thus, the spyware appears legitimate, and increase the likelihood it would be downloaded.
Links to articles are for interest and awareness and linking to or reposting external content does not endorse any service or product, likewise we are not responsible for the security of external links.
As usual, contact us to help assess where your risks lie and to ensure you are doing all you can do to keep you and your business secure.
Look out for our weekly ‘Cyber Tip Tuesday’ video blog and on our YouTube channel.
Cyber Weekly Flash Briefing 09 October 2020: Jersey based insurance firm Ardonagh hit with ransomware; Boards increase cyber investment; spike in romance scams; Amazon Prime Day phishing spike
Cyber Weekly Flash Briefing 09 October 2020: Jersey based insurance firm Ardonagh hit with ransomware; Boards increase cyber investment; spike in romance scams; cyber remains top business risk; ransomware surge as hackers take advantage of firms under pressure; Amazon Prime Day spurs phishing spike; new botnet wipes IoT devices; Emotet one of the most prevalent threats; Windows Error Reporting exploited
Links to articles are for interest and awareness and linking to or reposting external content does not endorse any service or product, likewise we are not responsible for the security of external links.
Jersey based insurance firm Ardonagh Group disabled 200 admin accounts as ransomware infection took hold
Jersey-headquartered insurance company Ardonagh Group has suffered a potential ransomware infection.
Reports indicated that the insurance firm had been forced to suspend 200 internal accounts with admin privileges as the "cyber incident" progressed through its IT estate.
The UK's second largest privately owned insurance broker, according to the Financial Times, Ardonagh Group has spent the year to date acquiring other companies.
The timing of the most recent attack is unfortunate: Ardonagh recently published its financials, showing a loss of £94.m, according to reports.
Why this matters:
Whilst there is nothing to suggest these attacks are linked this attack comes a week after US insurance giant Gallagher was also hit with ransomware.
No firm is immune to being hit with ransomware, no matter how good they think their defences are, and then it comes down to how well you had planned for ransomware happening and how capable you are to recover and get the business back on its feet.
Read more: https://www.theregister.com/2020/10/06/ardonagh_group_ransomware/ and https://www.insurancetimes.co.uk/news/ardonagh-data-breach-reported-to-information-commissioner/1434888.article
Boards Increase Investment in Cyber security in Face of Threats and Regulatory Fines
Board decisions on cyber security spending are slowly improving following the impact of regulatory fines and COVID-19.
According to research surveying 908 senior IT security decision makers working within organisations with more than 500 employees, 58% plan to add more security budget in the next 12 months.
Amid growing cyber threats and rising risks through the COVID crisis, CISOs report that boards are listening and stepping up with increased budget for cyber security, with 91% agreeing that their board adequately supports them with investment.
Retro-fixing of security to remote working tools was “a path and direction most organisations have been going down, however it was always a lower priority.”
COVID-19 has accelerated the investment into both cloud and remote working budgets, and this includes the need for secure remote access and the ability to access from any location. Having a CISO on the board is helping ensure technology that supports remote working environments are also secure by design.
Why this matters:
Boards are definitely listening and stepping up with increased budget for cyber security, however many firms still tend to view any investment as a cost rather than adding business value. There is still some way to go, boards mainly approve investments after a security incident or through fear of regulatory penalties for non-compliance which shows that cyber security investment decisions are more about insurance than about any desire to lead the field which, in the long run, limits the industry’s ability to keep pace with the cyber-criminals.
Read more: https://www.infosecurity-magazine.com/news/boards-increase-investment-fines/
Online Romance Scams Spike Under Lockdown
Police and banks are celebrating after revealing that £19 million in fraud was stopped in the first half of the year, although romance scams are reportedly on the rise.
Over 600 reports of romance scams were made each month in June, July and August, contributing to a 26% year-on-year increase in cases recorded by Action Fraud, according to Sky News.
These are typically confidence tricks where a vulnerable individual is contacted via a dating site and financially exploited or unwittingly used as a money mule.
Why this matters:
Over 19,400 such crimes were logged with the FBI last year, making it the second highest earner for cyber-criminals after business email compromise (BEC). Over $475 million was lost to romance scammers in 2019, the law enforcement agency said.
In the UK, losses are said to have exceeded £66 million between August 2019 and August 2020. As a result, various dating sites, banking groups and police are running a “Take Five” awareness campaign designed to warn users of the dangers posed by internet scammers.
The spike in romance scams coincided with COVID-19 lockdowns in the UK and much of the rest of the world, and a subsequent shift in crime and fraud online.
Action Fraud claimed it saw an increase in reported attacks in the first month of lockdown, to nearly 4000. UK Finance last month claimed that fraudsters are increasingly shifting their operations online.
However, Action Fraud also revealed this week that millions of pounds worth of fraud has been prevented so far this year thanks to a Banking Protocol first introduced three years ago.
The initiative enables banking staff in branches to alert their local police force when they suspect a customer is being scammed, for example if they are transferring or withdrawing large sums of money. It has been used to good effect to stop romance fraud, and impersonation scams, Action Fraud claimed.
In addition to the £19.3 million in fraud allegedly prevented, 100 arrests were made in the first half of the year.
Read more: https://www.infosecurity-magazine.com/news/online-romance-scams-spike-under/
WEF: Cyber-Attacks Remain Top Business Risk in the West
Cyber-attacks have dropped down the pecking order in terms of top global business risks but remain high on the priority list in North America and Europe, according to the latest World Economic Forum (WEF) data.
The annual Regional Risks for Doing Business report is compiled from over 12,000 responses from business leaders in 127 countries. They are presented with a pre-selected list of 30 global risks and asked to choose the five that they believe to be of most concern for doing business in their country over the next decade.
Why this matters:
Unsurprisingly given the current financial and healthcare crisis, the top two global risks were unemployment and spread of infectious disease, followed by fiscal crisis. Spread of infectious disease also topped the priority list for business leaders regionally in Europe, Eurasia and East Asia and the Pacific.
However, although cyber-attacks fell from second place globally last year to fourth, they are still top-of-mind in the West.
They were named the number one risk of the next decade by North American business leaders, garnering a share of 55% versus infectious diseases in second with 30%. Cyber-risk was placed second in Europe but first in the UK, with 56% versus fiscal crises in second with 45%.
Read more: https://www.infosecurity-magazine.com/news/wef-cyberattacks-top-business-risk/
Ransomware: Surge in attacks as hackers take advantage of organisations under pressure
The number of ransomware attacks has significantly grown over the past few months as cyber criminals look to cash in on security vulnerabilities opened up by the rise in remote working.
Researchers at cyber security company Check Point said the number of daily ransomware attacks across the globe has increased by half over the past three months – and that they've almost doubled in the US.
Why this matters:
One of the reasons ransomware attacks are on the rise is because of the swift switch to remote working that has forced many people to work from home for the first time, something that could leave them vulnerable to phishing emails and malware attacks, especially on a home network that likely won't be as secure as an enterprise environment.
Working from home also makes monitoring devices for malicious activity harder for information security teams than it would be if every user was under one roof, providing hackers with a better chance of going about their business unnoticed.
Amazon Prime Day Spurs Spike in Phishing, Fraud Attacks
Cyber criminals are tapping into Amazon’s annual discount shopping campaign for subscribers, Prime Day, with researchers warning of a recent spike in phishing and malicious websites that are fraudulently using the Amazon brand.
There has been a spike in the number of new monthly phishing and fraudulent sites created using the Amazon brand since August, the most significant since the COVID-19 pandemic forced people indoors in March, according to a new report published this week.
Why this matters:
As shoppers gear up for two days of great deals, cyber criminals are preparing to prey on the unwary, taking advantage of those who let their guard down to snap up bargains.
Prime Day actually happens over two days—this year the event falls on Oct. 13 to 14. Amazon Prime customers enjoy special sales and discounts on top brands to mark the biggest shopping event of the year on the online retail giant’s site.
Amazon last year yielded over $7 billion in sales during the 36-hour event, which could go even bigger this year due to “the decline of brick and mortar retail and the close proximity to the holidays,” researchers noted. Indeed, mandatory stay-at-home orders globally that began with the COVID-19 pandemic in March have significantly boosted Amazon’s business, a trend that shows no signs of abating.
Read more: https://threatpost.com/amazon-prime-day-spurs-spike-in-phishing-fraud-attacks/159960/
Microsoft warns of Android ransomware that activates when you press the Home button
A new strain of mobile ransomware abuses the mechanisms behind the "incoming call" notification and the "Home" button to lock screens on users' devices.
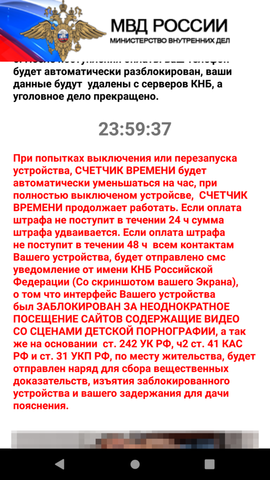
Named AndroidOS/MalLocker.B, the ransomware is hidden inside Android apps offered for download on online forums and third-party websites.
Just like most Android ransomware strains, MalLocker.B doesn't actually encrypt the victim's files but merely prevents access to the rest of the phone.
Once installed, the ransomware takes over the phone's screen and prevents the user from dismissing the ransom note — which is designed to look like a message from local law enforcement telling users they committed a crime and need to pay a fine.
Why this matters:
Ransomware posing as fake police fines has been the most popular form of Android ransomware for more than half a decade now.
Across time, these malware strains have abused various functions of the Android operating systems in order to keep users locked on their home screen.
Past techniques included abusing the System Alert window or disabling the functions that interface with the phone's physical buttons.
MalLocker.B comes with a new variation of these techniques.
The ransomware uses a two-part mechanism to show its ransom note.
The first part abuses the "call" notification. This is the function that activates for incoming calls to show details about the caller, and MalLocker.B uses it to show a window that covers the entire area of the screen with details about the incoming call.
The second part abuses the "onUserLeaveHint()" function. This function is called when users want to push an app into the background and switch to a new app, and it triggers when pressing buttons like Home or Recents. MalLocker.B abuses this function to bring its ransom note back into the foreground and prevent the user from leaving the ransom note for the home screen or another app.
The abuse of these two functions is a new and never-before-seen trick, but ransomware that hijacks the Home button has been seen before.
Suspected Chinese Hackers Unleash Malware That Can Survive OS Reinstalls
Chinese hackers may be using malware that can survive Windows OS reinstalls to spy on computers.
Security firm Kaspersky Lab uncovered the malware, which exploits a computer’s UEFI (Unified Extensible Firmware Interface) to continually persist on a Windows machine.
Why this matters:
Attacking the UEFI is pretty alarming because the software is used to boot up your computer and load the operating system. It also operates separately from your computer’s main hard drive, and usually resides in the motherboard’s SPI flash memory as firmware. As a result, any malicious process embedded in the UEFI can survive an operating system reinstall while evading traditional antivirus solutions. This attack shows that in exceptional cases actors are willing to go to great lengths in order to gain the highest level of persistence on a victim’s machine.
New HEH botnet can wipe routers and IoT devices
A newly discovered botnet contains code that can wipe all data from infected systems, such as routers, servers, and Internet of Things (IoT) devices.
Named HEH, the botnet spreads by launching brute-force attacks against any internet-connected system that has its Telnet ports (23 and 2323) exposed online.
If the device uses default or easy-to-guess Telnet credentials, the botnet gains access to the system, where it immediately downloads one of seven binaries that install the HEH malware.
Why this matters:
This HEH malware doesn't contain any offensive features, such as the ability to launch DDoS attacks, the ability to install crypto-miners, or code to run proxies and relay traffic for bad actors.
The only features present are a function that ensnares infected devices and coerces them to perform Telnet brute-force attacks across the internet to help amplify the botnet; a feature that lets attackers run Shell commands on the infected device; and a variation of this second feature that executes a list of predefined Shell operations that wipe all the device's partitions.
US Department of Homeland Security (DHS) warns that Emotet malware is one of the most prevalent threats today
The malware known as Emotet has emerged as “one of the most prevalent ongoing threats” as it increasingly targets state and local governments and infects them with other malware, the cybersecurity arm of the Department of Homeland Security said on Tuesday.
Why this matters:
Emotet was first identified in 2014 as a relatively simple trojan for stealing banking account credentials. Within a year or two, it had reinvented itself as a formidable downloader or dropper that, after infecting a PC, installed other malware. The Trickbot banking trojan and the Ryuk ransomware are two of the more common follow-ons. Over the past month, Emotet has successfully burrowed into Quebec’s Department of Justice and increased its onslaught on governments in France, Japan, and New Zealand. It has also targeted the Democratic National Committee and numerous other US state and local government agencies.
Hackers exploit Windows Error Reporting service in new fileless attack
A new fileless attack technique that abuses the Microsoft Windows Error Reporting (WER) service is the work of a hacking group that is yet to be identified.
According to researchers the attack vector relies on malware burying itself in WER-based executables to avoid arousing suspicion.
In a blog post on Tuesday the researchers said the new "Kraken" attack -- albeit not a completely novel technique in itself -- was detected on September 17.
A lure phishing document found by the research team was packaged up in a .ZIP file. Titled, "Compensation manual.doc," the file claims to contain information relating to worker compensation rights, but when opened, is able to trigger a malicious macro.
Why this matters:
The macro leads to a payload injected a process connected to the WER service and used by Microsoft to track and address operating system errors.
That reporting service, WerFault.exe, is usually invoked when an error related to the operating system, Windows features, or applications happens," Malwarebytes says. "When victims see WerFault.exe running on their machine, they probably assume that some error happened, while in this case they have actually been targeted in an attack.
Cyber Weekly Flash Briefing 04 September 2020: CEOs could become personally liable for cyber attacks, DDoS extortion, WordPress flaw exploited, Business Email Compromise now $80k, printers at risk
Cyber Weekly Flash Briefing 04 September 2020: CEOs could soon be personally liable for cyber attacks, DDoS Extorters Demand Ransoms from Firms, Hackers exploiting a critical WordPress flaw, Average Business Email Compromise (BEC) attempts are now $80k, Iran based Pioneer Kitten APT Sells Corporate Network Access, Nearly A Million Printers At Risk Of Attack - Thousands Hacked To Prove It
Links to articles are for interest and awareness and linking to or reposting external content does not endorse any service or product, likewise we are not responsible for the security of external links.
CEOs could soon be personally liable for cyberattacks
Within four years, the majority of CEOs will be held personally responsible for cyberattacks that lead to injury and other physical damage.
This is according to a new report from Gartner, which asserts that liability for cyber-physical security incidents will “pierce the corporate veil to personal liability” for 75 percent of CEOs by 2024.
Cyber-physical systems (CPS) are described as digital systems that interact with the physical world, such as IoT devices or operational technologies (OT).
“Regulators and governments will react promptly to an increase in serious incidents resulting from failure to secure CPSs, drastically increasing rules and regulations governing them,” said Katell Thielemann, Research Vice President at Gartner.
“In the US, the FBI, NSA and Cybersecurity and Infrastructure Security Agency (CISA) have already increased the frequency and details provided around threats to critical infrastructure-related systems, most of which are owned by private industry. Soon, CEOs won’t be able to plead ignorance or retreat behind insurance policies.”
Why this matters:
CPS attacks with fatalities will incur costs to businesses of more than $50 billion within the next three years, Gartner predicts. Irrespective of the value of human life, businesses are looking at major costs in terms of compensation, litigation, insurance, regulatory fines and reputation loss.
Technology leaders need to help CEOs understand the risks that CPSs represent and the need to dedicate focus and budget to securing them. The more connected CPSs are, the higher the likelihood of an incident occurring.
Read more: https://www.itproportal.com/news/ceos-could-soon-be-personally-liable-for-cyberattacks/
Global DDoS Extorters Demand Ransom from Firms
Security experts are warning of a new global DDoS-related extortion campaign targeting businesses operating in the e-commerce, finance and travel sectors.
Researchers said they had been tracking the threat actors since mid-August, with victims in North America, APAC and EMEA. Emails are typically delivered claiming to come from state-sponsored groups such as Fancy Bear and Lazarus Group, as well as the “Armada Collective.”
The latter group has been linked to similar extortion emails sent in previous years.
The ransom emails threaten to launch DDoS attacks against the recipient organization of over 2Tbps, if payment of anywhere between 10 and 20BTC ($113,000-226,000) is not made. They also threaten to increase the ransom by 10BTC for each deadline missed.
Also included in the messages are the Autonomous System Numbers (ASNs) or IP addresses of servers or services that the group says it will target if their demands are not met.
Why this matters:
DDoS attacks take businesses legitimate online operations offline by flooding them with traffic such that legitimate traffic can’t get through, or they are so swamped with traffic that services can’t cope. Depending on the type of business and how reliant they are on their online presence these types of attacks could prevent firms from operating entirely.
Recipients of the emails were urged not to pay the ransom
Read more: https://www.infosecurity-magazine.com/news/global-ddos-extorters-ransom-notes/
Hackers are exploiting a critical flaw affecting >350,000 WordPress sites
Hackers are actively exploiting a vulnerability that allows them to execute commands and malicious scripts on Websites running File Manager, a WordPress plugin with more than 700,000 active installations, researchers said on Tuesday. Word of the attacks came a few hours after the security flaw was patched.
Why this matters:
Attackers are using the exploit to upload files hidden in an image, which from there provides a convenient interface that allows them to run commands in the directory where the File Manager plugin resides. Hackers may be able to exact more damage by uploading scripts that can carry out actions on other parts of a vulnerable site.
Phishing attacks surge during the pandemic
In yet another example of cyber criminals exploiting world events, the frequency of phishing threats has risen considerably since the start of the pandemic, with companies experiencing an average of 1,185 attacks every month.
New research reveals that more than half (53 percent) of over 300 IT professionals surveyed by Cyber security Insiders say they had witnessed an increase in phishing activity since the start of the COVID-19 pandemic.
Why this matters:
The report also shows that 38 percent of respondents report that a co-worker has fallen victim to an attack within the last year. As a result, 15 percent of organizations are now left spending anywhere from one to four days remediating malicious attacks during what is already a difficult time for many.
Read more: https://betanews.com/2020/09/01/phishing-surges-during-pandemic/
Average Business Email Compromise (BEC) attempts are now $80k, but one group is aiming for $1.27m per attack
BEC scammer groups are growing more brazen. The average sum that a BEC group will try to steal from a targeted company is now around $80,000 per attack, according to an industry report published on Monday.
The number is up from $54,000, the average sum that BEC groups tried to obtain from victims in Q1 2020, as reported by the Anti-Phishing Working Group (APWG), an industry coalition made up of more than 2,200 organizations from the cyber-security industry, government, law enforcement, and NGOs sector.
One of the largest industry group of its kind, the APWG has been releasing quarterly reports on the state of phishing operations since 2004.
Why this matters:
Most of these reports have usually centred on email phishing attacks that focus on stealing login credentials and distributing malware. However, since the mid-2010s, BEC fraud has been slowly taking more and more space in APWG's reports, as BEC fraud has become today's top cybercrime trend.
BEC, or Business Email Compromise (BEC) scams, usually begin with phishing, with an email sent to a company's employee. The end goal is to dupe the employee into paying fake invoices or transferring funds to an account controlled by the attackers.
Iran based Pioneer Kitten APT Sells Corporate Network Access
An APT (Advanced Persistent Threat) group known as Pioneer Kitten, linked to Iran, has been spotted selling corporate-network credentials on hacker forums.
Pioneer Kitten is a hacker group that specialises in infiltrating corporate networks using open-source tools to compromise remote external services. Researchers observed an actor associated with the group advertising access to compromised networks on an underground forum in July, according to a blog post earlier this week.
Pioneer Kitten’s work is related to other groups either sponsored or run by the Iranian government, which were previously seen hacking VPNs and planting backdoors in companies around the world.
Why this matters:
The credentials would let other cybercriminal groups and APTs perform cyberespionage and other nefarious cyber-activity. It is also noteworthy to see a group operating on behalf of or closed with a Nation State, in this case Iran, appearing to potential attempt to diversify their revenue streams through sales of stolen credentials.
Read more: https://threatpost.com/pioneer-kitten-apt-sells-corporate-network-access/158833/
Nearly A Million Printers At Risk Of Attack, Thousands Hacked To Prove It
Roughly 28,000 printers recently gave their owners an unexpected lesson in cybersecurity. Seemingly unprompted, the printers whirred to life and produced a 5-step guide to keeping hackers at bay.
“This printer has been hacked,” the message began ominously. Fortunately for the “victims” it was a group of ethical hackers behind the attack. A team of researchers from CyberNews was out to remind the public about the potential peril of connected devices.
To get the ball rolling, the team scoured the globe for printers that were vulnerable. They found more than 800,000 in total using a search engine called Shodan.
Shodan is a tool that’s leaned on by both security researchers and cyber criminals. In the past it’s been used to identify thousands of at-risk surveillance cameras, security alarm systems and hundreds of wind turbines and solar devices.
Why this matters:
Vulnerable devices within your networks can present a vulnerability to other devices on your network too and can be an easy point of entry for attackers.
Many firms do a good job of updating desktops and laptops when operating system updates come out, but too many firms neglect networking devices such as routers, modems and switches, and other devices on their networks such as printers.
Read more: https://www.forbes.com/sites/leemathews/2020/08/31/800000-printers-vulnerable-28000-hacked/#4b7c9b87d8a9
or: https://cybernews.com/security/we-hacked-28000-unsecured-printers-to-raise-awareness-of-printer-security-issues/
WhatsApp reveals six previously undisclosed vulnerabilities on new security site
Facebook -owned WhatsApp has revealed six previously undisclosed vulnerabilities, which the company has now fixed. The vulnerabilities are being reported on a dedicated security advisory website that will serve as the new resource providing a comprehensive list of WhatsApp security updates and associated Common Vulnerabilities and Exposures (CVE).
WhatsApp said five of the six vulnerabilities were fixed in the same day, while the remaining bug took a couple of days to remediate. Although some of the bugs could have been remotely triggered, the company said it found no evidence of hackers actively exploiting the vulnerabilities.
Why this matters:
WhatsApp is one of the world’s most popular apps, with more than two billion users around the world. But it’s also a persistent target for hackers, who try to find and exploit vulnerabilities in the platform. As with all software updates should be applied as soon as possible to ensure that fixes that remediate known vulnerabilities are fixed.
Read more: https://techcrunch.com/2020/09/03/whatsapp-security-flaws/
Attackers are trying to exploit a high-severity zero day in Cisco gear
Telecoms and data-centre operators take note: attackers are actively trying to exploit a high-severity zero day vulnerability in Cisco networking devices, the company warned over the weekend.
The security flaw resides in Cisco’s iOS XR Software, an operating system for carrier-grade routers and other networking devices used by telecommunications and data-centre providers. In an advisory published on Saturday, the networking-gear manufacturer said that a patch is not yet available and provided no timeline for when one would be released.
Why this matters:
Zero days do not yet have patches available although the vulnerability is publicly known and in some cases, as in this case, already being targeted by malicious actors.
Cyber Weekly Flash Briefing 28 August 2020: cyber crime cost per minute $11.4m by 2021, Trend block 28 billion Cyber Threats H1 2020, Malicious Attachments Top Threat, NK hackers ramp up bank heists
Cyber Weekly Flash Briefing 28 August 2020: global cost of cybercrime per minute to reach $11.4 million by 2021, Trend blocks 28 Billion Cyber-Threats in H1 2020, Malicious Attachments Remain a Cyber Criminal Threat Vector Favourite, 80% of Exploits Published Faster than CVEs, North Korean hackers ramp up bank heists
Links to articles are for interest and awareness and linking to or reposting external content does not endorse any service or product, likewise we are not responsible for the security of external links.
The global cost of cyber crime per minute to reach $11.4 million by 2021
Cyber crime costs organisations $24.7, YOY increase of more than $2 every minute, according to a new report. It will also have a per-minute global cost of $11.4 million by 2021, a 100% increase over 2015.
The report covers the top threats facing today’s organizations, which are proliferating at a clip of 375 per minute, and reflects the current surge in attacks leveraging the COVID-19 pandemic.
Other malicious activity
1.5 attacks on computers with an Internet connection per minute
375 new threats per minute
16,172 records compromised per minute
1 vulnerability disclosed every 24 minutes
5.5 vomain infringements detected per minute
1 Magecart attack every 16 minutes
1 COVID-19 blacklisted domain every 15 minutes
35 COVID-19 spam emails analysed per minute
Why this matters:
The sheer scale of today’s threat activity is driven by a variety of factors, including that cyber crime is easier than ever to participate in and better threat technology makes cyber criminals more effective and wealthier than in the past.
Read more: https://www.helpnetsecurity.com/2020/08/28/global-cost-of-cybercrime-per-minute/
Trend Micro Blocks 28 Billion Cyber-Threats in H1 2020
Trend Micro blocked nearly nine million COVID-related threats in the first half of 2020, the vast majority of which were email-borne, it revealed in a new mid-year roundup report.
The security giant said it detected 8.8 million cyber-threats leveraging the virus as a lure or theme for attacks, 92% of which were delivered by spam emails.
However, the figure represents less than 1% of the total of 27.8 billion threats the vendor blocked in the first six months of the year.
This chimes with data from Microsoft and others which suggests that cyber-criminals merely repurposed existing campaigns to take advantage of COVID-19. As such, the pandemic itself has not prompted a rise in overall cyber crime levels.
However, the data does show conclusively that email remains the number one threat vector: 93% of total blocked threats were heading for users’ inboxes.
As part of this trend, Business Email Compromise (BEC) detections increased by 19% from the second half of 2019. This is due in part to scammers trying to capitalize on distracted home workers who may be more exposed to social engineering, and less able to check with colleagues if a money transfer request is legitimate or not.
Why this matters:
Email remains the number one threat to all firms and by far the most likely way firms will end up being breached, and this depends on your users being aware and switched on and efficient at spotting email borne attacks as technology solutions alone are not good at blocking email based attacks. Criminals will always exploit current events and crises to improve their effectiveness of their attacks.
Read more: https://www.infosecurity-magazine.com/news/trend-micro-blocks-28-billion/
Malicious Attachments Remain a Cyber Criminal Threat Vector Favourite
Malicious attachments continue to be a top threat vector in the cybercriminal world, even as public awareness increases and tech companies amp up their defences.
While attachment threat vectors are one of the oldest malware-spreading tricks in the books, email users are still clicking on malicious attachments that hit their inbox, whether it’s a purported “job offer” or a pretend “critical invoice.”
The reason why threat actors are still relying on this age-old tactic, researchers say, is that the attack is still working. Even with widespread public awareness about malicious file attachments, attackers are upping their game with new tricks to avoid detection, bypass email protections and more. The attack vector is still widespread enough where tech giants are re-inventing new ways to try to stomp it out, with Microsoft just this week rolling out a feature for Office 365 that aims to protect users against malicious attachments sent via email, for instance.
Why this matters:
Email attachments, such as PDF or Office files, are an easy vector to deliver malicious content to end users. For enterprises, the risk is that malicious actors can use these attachments to establish a toe-hold at the outermost edges of the enterprise, and then wait and wind their way to the crown jewels in their data stores.
Read more here: https://threatpost.com/malicious-attachments-remain-a-cybercriminal-threat-vector-favorite/158631/
The State of Exploit Development: 80% of Exploits Publish Faster than CVEs
With the ever-increasing number of new vulnerabilities, vulnerability management becomes one of the most critical processes in ensuring continuous business operation. While it is clear that timely patching is essential, it’s also important to know quantitatively how a delay could increase risk. What are the chances that attackers breach an organisation using a CVE just disclosed or using an unknown (zero-day) vulnerability? To understand the state of vulnerability disclosure and exploit development, researchers analysed 45,450 the publicly available exploits in the Exploit Database at the time of this writing. The research correlated the exploit data with vulnerability and patch information to study exploit development in multiple facets.
The research reveals that:
Of the 45,450 public exploits in Exploit Database, there are 11,079 (~26%) exploits in Exploit Database that have mapped CVE numbers.
Among those 11,079 exploits:
14% are zero-day (published before the vendors release the patch), 23% are published within a week after the patch release and 50% are published within a month after the patch release. On average, an exploit is published 37 days after the patch is released. Patch as soon as possible – the risk of a vulnerability being exploited increases quickly after vendors release the patches.
80% of public exploits are published before the CVEs are published. On average, an exploit is published 23 days before the CVE is published. Software and hardware may also have vulnerabilities with public exploits that don’t have CVEs. Check security updates from vendors frequently and apply updates as soon as possible.
Analysis of the entire CVE list since 1999 found that, on average, a CVE is published 40 days after its CVE-ID is assigned. Of the 177,043 entries analysed more than 10,000 CVEs have been in “reserved” status for more than two years. It shows that there is a long delay between vulnerability discovery and CVE publication.
Why this matters:
Patches should always be applied as soon as possible, exploits either follow very soon after vulnerability disclosure but as this study shows sometimes vulnerabilities are being exploited before fixes are released. The longer between fixes being released and being applied the more vulnerable you are to attack.
Read more here: https://unit42.paloaltonetworks.com/state-of-exploit-development/
Forget your space-age IT security systems. It might just take a $1m bribe and a willing employee to be pwned
A Russian citizen is accused of flying to America in a bid to bribe a Tesla employee to infect their bosses' IT network with ransomware.
Egor Kriuchkov has been charged with one count of conspiracy to intentionally cause damage to a protected computer. He was nabbed by the Feds at Los Angeles airport and is behind bars awaiting trial.
It is claimed Kriuchkov, 27, was the point man of a plot to get data-stealing malware onto the network of an unspecified US company in Nevada and then use the lifted data to extort the corporation for millions of dollars: paid up, or the internal files get leaked and file systems scrambled.
To do this, Kriuchkov and his associates back in Russia had recruited a worker at the business, it is claimed, and promised to pay $500,000 for placing the malware onto its network. The bribe was later increased to $1m to persuade the employee, along with an $11,000 advance, yet instead he went to his bosses, and the FBI was brought in, we're told.
According special agent Michael Hughes, in late July Kriuchkov travelled from Russia to Reno, Nevada, where the employee worked, and over the early weeks of August tried to win over the employee to join the conspiracy. This included a night out for the worker and friends at a Lake Tahoe resort, followed by Kriuchkov pulling the worker aside and convincing them to play a key role in the operation, it is claimed.
Why this matters:
Again this shows that employees are more likely than your technical systems to be exploited by malicious actors, fortuitously for Tesla the employee didn’t take the bribe but many staff in different organisations would be tempted. Imagine if the employee that was approached was already feeling disgruntled against their employer.
Read more here: https://www.theregister.com/2020/08/26/russian_malware_plot/
Ex-Cisco staffer charged with deliberately deleting 400+ VMs
A disgruntled former Cisco employee has pleaded guilty to intentionally deleting hundreds of the networking firm's virtual machines (VMs), according to an IT News report.
Sudhish Kasaba Ramesh, an ex-Cisco engineer who left the company in April 2018, accessed the firm's AWS environment months later and deleted a total of 456 VMs, which the company used to run the WebEx Teams application.
In a statement, issued before a US federal court in San Jose by the US Department of Justice and the FBI, it was said that Ramesh “intentionally accessed a protected computer without authorization and recklessly caused damage”.
“During his unauthorized access, Ramesh admitted that he deployed a code from his Google Cloud Project account that resulted in the deletion of 456 virtual machines for Cisco’s WebEx Teams application, which provided video meetings, video messaging, file sharing, and other collaboration tools,” the statement said.
Why this matters:
Insiders will always be amongst the biggest threats to every organisation and the damage a disgruntled employee or former employer could cause should never be underestimated. Any time a member of staff leaves an organisation it must be ensured that they no longer have access to any accounts accessed in the course of the performing their duties, and doubly so for accounts with privileged or elevated permissions, for the very reason they could do so much damage.
Read more: https://www.itproportal.com/news/ex-cisco-staffer-charged-with-deliberately-deleting-400-vms/
North Korean hackers ramp up bank heists: U.S. government cyber alert
North Korean hackers are tapping into banks around the globe to make fraudulent money transfers and cause ATMs to spit out cash, the U.S. government warned on Wednesday.
A technical cyber security alert jointly written by four different federal agencies, including the Treasury Department and FBI, said there had been a resurgence in financially motivated hacking efforts by the North Korean regime this year after a lull in activity.
“Since February 2020, North Korea has resumed targeting banks in multiple countries to initiate fraudulent international money transfers and ATM cash outs,” the warning reads.
U.S. law enforcement titled the hacking campaign “Fast Cash” and blamed North Korea’s Reconnaissance General Bureau, a spy agency, for it. They described the operation as going on since at least 2016 but ramping up in sophistication and volume recently.
Why this matters:
Over the last several years, North Korea has been blamed by U.S. authorities and private sector cyber security companies for hacking numerous banks in Asia, South America and Africa.
North Korean cyber actors have demonstrated an imaginative knack for adjusting their tactics to exploit the financial sector as well as any other sector through illicit cyber operations.
Read more here: https://www.reuters.com/article/us-cyber-usa-north-korea-idUSKBN25M2FU
New Zealand stock exchange resumes trade after cyber attacks, government activates security systems
New Zealand’s stock exchange resumed trading on Friday, after facing disruptions for four consecutive days in the wake of cyber attacks this week, while the government said national security systems had been activated to support the bourse.
There is no clarity on who was behind these two “offshore” attacks, but the failure to stop them has raised questions about New Zealand’s security systems, experts said.
NZX Ltd had to halt trading until afternoon on Friday, after crashing earlier due to network connectivity issues, marking the fourth day that trading has been hit.
Why this matters:
Organisations of all sizes are vulnerable to attacks, larger firms are vulnerable because of the sheer number of users and the complexity of their systems, smaller firms because they often lack maturity and don’t have the most appropriate controls and protections in place. Firms also need to make sure they have plans in place to recover and return to operational effectiveness as quickly as possible.
Read more here: https://www.reuters.com/article/uk-nzx-cyber-idUSKBN25O03Q
Cyber Weekly Flash Briefing 07 August 2020: INTERPOL warn on alarming pace of cyber crime, Canon ransomware, Garmin paid ransom, TV Licence fraud targets elderly, Netgear won’t patch vuln routers
Cyber Weekly Flash Briefing 07 August 2020: INTERPOL warning on “Alarming Pace” of cyber crime, Capital One fined $80m, Canon ransomware attack, Garmin reportedly paid multimillion ransom, Over-75s warned of rise in TV Licence 'phishing' fraud, Netgear Won’t Patch 45 Router Models Vulnerable to Serious Flaw
Links to articles are for interest and awareness and linking to or reposting external content does not endorse any service or product, likewise we are not responsible for the security of external links.
INTERPOL: Cyber crime Growing at an “Alarming Pace” Due to #COVID19
Cyber crime is growing at an “alarming pace” as a result of the ongoing COVID-19 crisis and is expected to accelerate even further, a new report from INTERPOL has found.
It revealed the extent to which cyber-criminals are taking advantage of the increasing reliance on digital technology over recent months. This includes the rapid shift to home working undertaken by many organisations, which has involved the deployment of remote systems and networks, often insecurely.
Based on feedback from member countries, INTERPOL said that during the COVID-19 period, there has been a particularly large increase in malicious domains (22%), malware/ransomware (36%), phishing scams/fraud (59%) and fake news (14%).
Threat actors have revised their usual online scams and phishing schemes so that they are COVID-themed, playing on people’s economic and health fears.
Why this matters:
Increases in malicious activity is always a concern, especially when firms don’t realise how bad the situation is already and fail to grasp how much worse it is getting. Cyber criminals have gone through an industrial revolution and have built criminal organisations to rival some of the biggest legitimate business empires. Increases in threats require and increase in defensive capability, across IT, people and governance, to counter this rising tide.
Read more: https://www.infosecurity-magazine.com/news/cybercrime-growing-alarming-pace/
Capital One fined $80m for data breach
Capital One, one of the top five credit card issuers by balances in the US, has been fined $80m and ordered to improve internal controls after regulators identified a string of failings that allowed hackers to obtain the personal data of more than 106m customers and credit card applicants last year.
The bank was found to have failed to establish effective risk assessment processes prior to migrating significant information technology operations to the public cloud, as well as failing to quickly correct deficiencies.
The data breach exposed names, addresses, phone numbers, self-reported income, credit scores and payment history, as well as some people’s social security numbers.
It has become a cautionary tale for banks migrating their data from their own physical IT to the kind of virtual clouds that the Capital One data was hacked from.
Why this matters:
Moving to the cloud can open up new risks and misconfigurations can go undetected until they are exploited by malicious actors. It is important to make sure you know where the weaknesses and vulnerabilities are before someone else does, and this included cloud infrastructure.
Read more: https://www.ft.com/content/a730c6a0-c362-4664-a1ae-5faf84912f20
Canon confirms ransomware attack in internal memo
Canon appears to be latest in a number of large high profile firms in recent weeks to suffer a ransomware attack that has had an impact on numerous services, including Canon's email, Microsoft Teams, USA website, and other internal applications. In an internal alert sent to employees, Canon has disclosed the ransomware attack and working to address the issue.
Researchers were alerted by a suspicious outage on Canon's image.canon cloud photo and video storage service resulting in the loss of data for users of their free 10GB storage feature.
However, the final status update was strange as it mentions that while data was lost, "there was no leak of image data." This led BleepingComputer to believe there was more to the story and that they suffered a cyberattack.
Why this matters:
Any firm of any size can fall victim to ransomware and recovering can be time consuming, expensive and cause significant reputational damage. These attacks invariably stem from users clicking on links in phishing emails, something that IT departments and technical controls aren’t capable of defending against on their own.
Read more: https://www.bleepingcomputer.com/news/security/canon-confirms-ransomware-attack-in-internal-memo/
Garmin reportedly paid multimillion-dollar ransom after suffering cyberattack
Following on from Canon being the latest high profile victim, reports indicate that fitness wearable and satellite navigation brand Garmin paid millions of dollars in ransom after an attack took many of its products and services offline last month. The payment was reportedly made through a ransomware negotiation company in order for Garmin to recover data held hostage as a result of the attack.
It was reported last week that Garmin had received a decryption key to access data encrypted by the virus, and that the initial ransom demand was for $10 million.
Why this matters:
If a company had to resort to paying the ransom then it can be inferred that they were unable to recover their data, had insufficient backups or had never tested recovering from backups and when they needed to for real found they were unable. It’s too late to find out when you need something that you don’t have it.
If no firm or individual paid ransoms this problem would go away. For as long as even a small number of firms and individuals pay this will continue to be a massive problem, affecting everyone.
Read more: https://www.theverge.com/2020/8/4/21353842/garmin-ransomware-attack-wearables-wastedlocker-evil-corp
Google: Eleven zero-days detected in the wild in the first half of 2020
According to data collected by Google's Project Zero security team, there have been 11 zero-day vulnerabilities exploited in the wild in the first half of the year.
The current number puts 2020 on track to have just as many zero-days as 2019 when Google security researchers said they tracked 20 zero-days all of last year.
Details about these zero-days have been obtained from a spreadsheet managed by Google security researchers, which the company made public available earlier this year. The spreadsheet contains Google's internal statistics about in-the-wild zero-day usage going as far back as 2014, when the company began tracking said stats.
Why this matters:
Zero-days are vulnerabilities for which fixes have not yet been made available and as such as difficult to defend against. Good security is all about having multiple layers of controls and if you have good procedural, people and governance controls in place this should still go a good way to helping to defend against zero-days.
As soon as security updates are made available they should ideally be tested and applied on all applicable devices as soon as possible to prevent vulnerabilities from being exploited.
TeamViewer flaw could be exploited to crack users’ password
A high-risk vulnerability (CVE-2020-13699) in TeamViewer for Windows could be exploited by remote attackers to crack users’ password and, consequently, lead to further system exploitation.
TeamViewer is an application that is used primarily for remote access to and control of various types of computer systems and mobile devices, but also offers collaboration and presentation features (e.g., desktop sharing, web conferencing, file transfer, etc.)
Since the advent of COVID-19, enterprise use of the software has increased due to many employees being forced to work from home.
Why this matters:
Credentials stolen from any successful breach are likely to be used in credential stuffing attacks (where the same usernames and passwords are reused) against other sites and services.
Read more: https://www.helpnetsecurity.com/2020/08/06/cve-2020-13699/
Qualcomm chip vulnerability puts millions of phones at risk
Smartphone devices from the likes of Google, LG, OnePlus, Samsung and Xiaomi are in danger of compromise by cyber criminals after 400 vulnerable code sections were uncovered on Qualcomm’s Snapdragon digital signal processor (DSP) chip, which runs on over 40% of the global Android estate.
To exploit the vulnerabilities, a malicious actor would merely need to convince their target to install a simple, benign application with no permissions at all.
Why this matters:
The vulnerabilities leave affected smartphones at risk of being taken over and used to spy on and track their users, having malware and other malicious code installed and hidden, or even being bricked outright. Hopefully a fix will be forthcoming but it looks like it might be months before this fix is widely available.
Read more here: https://www.computerweekly.com/news/252487274/Qualcomm-chip-vulnerability-puts-millions-of-phones-at-risk
Over-75s warned of rise in TV Licence 'phishing' fraud
Over-75s awaiting letters about their new licence fee payments are falling victim to fraudsters, it has emerged.
The BBC has told 4.5 million pensioners to expect a letter from TV Licensing advising them on how to set up payment, as the free scheme for over-75s ended on July 31.
But the corporation has not given an indication of when the communication will arrive or what the wording will be, and in the meantime pensioners are being duped by scam emails which purport to be official.
The National Cyber Security Centre, part of GCHQ, said the number of licence fee “phishing” emails had risen in July, compared to previous months, and it was working hard to block them.
A spokesman said: “It is despicable that criminals are targeting over-75s in this way. TV Licensing would never ask for payment details over an email, so as soon as we were alerted to the scam messages sent in this callous campaign, they were immediately blocked.
Why this matters:
Cyber criminals are unscrupulous and will happily target the most vulnerable members of our society. If you have elderly relatives make them aware of these scams and encourage them not to respond for requests sent via email.
Read more: https://www.telegraph.co.uk/news/2020/08/03/over-75s-warned-rise-tv-licence-phishing-fraud/
Netgear Won’t Patch 45 Router Models Vulnerable to Serious Flaw
Netgear will not patch 45 router models that are vulnerable to a high-severity remote code execution flaw, the router company revealed last week. However, the company says that routers that won’t receive updates are outdated or have reached EOL (End of Life).
The remote code execution vulnerability in question, which was disclosed June 15, allows network-adjacent attackers to bypass authentication on vulnerable Netgear routers – sans authentication. The high-severity flaw affects 79 Netgear Wi-Fi routers and home gateway models – but Netgear says that 45 of those router models are outside of its “security support period.”
Why this matters:
If you are using a Netgear device ensure that it is not in the list of devices that are no longer supported and if necessary replace it with a different router that is supported. If the device you own is still supported you should log into the web interface and ensure that it is updated to the most recent version of firmware to include any security updates.
Many people never update the firmware on their networking devices at home and this means that there can be a significant number of significant security vulnerabilities that have gone unfixed jeopardising the security of any devices connected to that router. If you don’t know how to update home networking devices contact someone who can help you to do this.
Read more: https://threatpost.com/netgear-wont-patch-45-router-models-vulnerable-to-serious-flaw/157977/
Cyber Weekly Flash Briefing 31 July 2020: 386M user records stolen, Twitter spear-phishing, Garmin may have paid ransom, 27% of consumers hit with Covid19 phishing scams, Netflix phishing scam
Cyber Weekly Flash Briefing 31 July 2020: 386M user records stolen, Twitter says attack was spear-phishing, Criminals still exploiting COVID19, Netwalker ransomware, Garmin may have paid ransom, QNAP NAS devices infected, Hackers exploit networking vulns, 27% of consumers hit with pandemic-themed phishing scams, New Netflix phishing scam
Links to articles are for interest and awareness and linking to or reposting external content does not endorse any service or product, likewise we are not responsible for the security of external links.
386 million user records stolen in data breaches — and they're being given away for free
A notorious hacker or group of hackers is giving away copies of databases said to contain 386 million user records, after posting links to the databases on a marketplace used by cyber criminals.
The threat actor, who goes by the name ShinyHunters, claims to have data stolen from 18 different websites in the past seven months. According to reports, ShinyHungers last week began uploading the databases to a forum where anyone can download them free of charge.
ShinyHunters is believed to have played a role in high-profile data breaches at HomeChef, Promo.com, Mathway, Chatbooks, Dave.com, Wattpad and even Microsoft's GitHub account. Many of these records were previously offered for sale online.
Why this matters:
Any details stolen from one site or service will be used against other sites and services, this is why it is critical that passwords are not reused across different sites and that all passwords are unique. Using multi factor authentication is also very effective at safeguarding against these types of attacks.
Read more here: https://www.tomsguide.com/news/shinyhunters-breach-giveaway
Twitter says spear-phishing attack on employees led to breach
Twitter said a large hack two weeks ago targeted a small number of employees through a phone “spear-phishing” attack.
The social media platform said the hackers targeted about 130 accounts, tweeted from 45, accessed the inboxes of 36, and were able to download Twitter data from seven.
Attackers also targeted specific employees who had access to account support tools, Twitter said. The company added it has since restricted access to its internal tools and systems.
Twitter suffered a major security breach on 15 July that saw hackers take control of the accounts of major public figures and corporations, including Joe Biden, Barack Obama, Elon Musk, Bill Gates, Jeff Bezos and Apple.
The hack unfolded over the course of several hours, and in the course of halting it, Twitter stopped all verified accounts from tweeting – an unprecedented measure.
Publicly available blockchain records show the apparent scammers received more than $100,000 worth of cryptocurrency.
Why this matters?
It is nearly always a lot easier for attackers to attack your users than it is to attack your systems. IT controls alone cannot protect against social engineering attacks so making sure your staff are trained so they don’t fall for social engineering attacks is a critical part of your defence.
Read more here: https://www.theguardian.com/technology/2020/jul/30/twitter-breach-hackers-spear-phishing-attack
Cyber-Criminals Continue to Exploit #COVID19 During Q2
Cyber-criminals’ exploitation of the COVID-19 pandemic to target individuals and businesses has continued unabated during the second quarter of 2020, according to one Cyber Security firm’s Q2 2020 Threat Report published today. The findings highlight how the crisis is defining the cybersecurity landscape in Q2 in a similar way as it did in Q1 after the pandemic first struck.
The firm observed a continuous focus on phishing using COVID-19 lures in this period. This included criminals taking advantage of the rise in online shopping that has occurred during the pandemic, with a 10-fold increase in phishing emails impersonating one of the world’s leading package delivery services found in comparison to Q1.
The shift to remote working as a result of the pandemic has also led to increased targeting of Remote Desktop Protocol’s in recent months.
Ransomware tactics were found to be “rapidly developing” in this period, with operators moving away from doxing and random data leaking towards auctioning the stolen data on dedicated underground sites.
Why does this matter?
The Coronavirus crisis gave criminals an efficient lure to bait phishing emails with and for as long as it is working they will continue to exploit this crisis. It’s like we always say “cyber criminals will never let a good crisis or tragedy go to waste”
Read more here: https://www.infosecurity-magazine.com/news/cyber-criminals-exploit-covid/
FBI Releases Flash Alert on Netwalker Ransomware
The US Federal Bureau of Investigations (FBI) released a flash alert in which it warned organisations about the dangers of Netwalker ransomware.
The FBI said that it had received notifications of attacks involving Netwalker against U.S. and foreign government organisations along with entities operating in the healthcare and education sectors.
In its alert, the FBI noted that those responsible for Netwalker had used COVID-19 phishing emails and unpatched vulnerabilities affecting VPN apps to gain entry into an organisation. The malicious actors had then used their crypto-malware to harvest administrator credentials and steal data from their victims. Ultimately, the attackers uploaded that stolen information to a file-sharing service.
Once they had come into possession of a victim’s data, the nefarious individuals activated the ransomware’s encryption routine. This step led the threat to encrypt all connected Windows-based devices and information before dropping a ransom note on the infected machine.
Why does this matter?
Ransomware remains one of the biggest risks for all firms, organisations and individuals, and the majority of the time the ransomware infection will stem from a phishing email that a user within an organisation clicked on. As with all social engineering attacks IT controls alone are of limited effectiveness and defending against these attacks comes down to educating your users and instilling in them the importance of the role they play in defending an organisation.
Read more here: https://www.tripwire.com/state-of-security/security-data-protection/fbi-releases-flash-alert-on-netwalker-ransomware/
Garmin may have paid hackers ransom, reports suggest
Fitness wearable and Navtech supplier Garmin may have given in to the demands of cyber criminals who encrypted its systems with ransomware, according to news reports that suggest the firm has obtained a decryption key to recover its files, strongly suggesting it has either paid up, or brokered some kind of deal.
In a statement issued four days after its services first went offline, Garmin finally confirmed it had been the victim of a cyber attack, having previously limited its response to saying it was experiencing an outage. It has not yet confirmed it was the victim of a ransomware incident, although this is now all but certain.
A spokesperson said: “Garmin today announced it was the victim of a cyber attack that encrypted some of our systems on July 23, 2020. As a result, many of our online services were interrupted including website functions, customer support, customer-facing applications, and company communications. We immediately began to assess the nature of the attack and started remediation,” said the firm.
“We have no indication that any customer data, including payment information from Garmin Pay, was accessed, lost or stolen. Additionally, the functionality of Garmin products was not affected, other than the ability to access online services.
Why does this matter?
Ransomware can affect firms of any size, from the smallest to the largest, no firm or organisation is immune and even firms that are spending millions or tens of millions on advanced protections and controls can still fall victim. These types of attacks go after the people working for an organisation, not the organisations technical infrastructure and technical controls are of limited use in defending against these types of attacks. An organisation needs to ensure their users are efficient at spotting phishing emails, it only takes one user clicking on one malicious email to take down a multinational corporation.
Read more here: https://www.computerweekly.com/news/252486775/Garmin-may-have-paid-hackers-ransom-reports-suggest
Cyber-security agencies from the UK and the US say 62,000 QNAP NAS devices have been infected with the QSnatch malware
The UK NCSC and US CISA published a joint security alert this week about QSnatch, a strain of malware that has been infecting network-attached storage (NAS) devices from Taiwanese device maker QNAP.
In alerts by the United States Cybersecurity and Infrastructure Security Agency (CISA) and the United Kingdom's National Cyber Security Centre (NCSC), the two agencies say that attacks with the QSnatch malware have been traced back to 2014, but attacks intensified over the last year when the number of reported infections grew from 7,000 devices in October 2019 to more than 62,000 in mid-June 2020.
Of these, CISA and the NSCS say that approximately 7,600 of the infected devices are located in the US, and around 3,900 in the UK.
Why this matters?
Vulnerable devices can be used to steal credentials (usernames and passwords) and exfiltrate information from devices on the network. It is important to keep devices up to date with the latest security patches to close any vulnerabilities before they can be exploited.
Read more here: https://www.zdnet.com/article/cisa-says-62000-qnap-nas-devices-have-been-infected-with-the-qsnatch-malware/
Hackers actively exploit high-severity networking vulnerabilities
Hackers are actively exploiting two unrelated high-severity vulnerabilities that allow unauthenticated access or even a complete takeover of networks run by FTSE100/Fortune 500 companies and government organisations.
The most serious exploits are targeting a critical vulnerability in F5’s Big-IP advanced delivery controller, a device that’s typically placed between a perimeter firewall and a Web application to handle load balancing and other tasks. The vulnerability, which F5 patched three weeks ago, allows unauthenticated attackers to remotely run commands or code of their choice. Attackers can then use their control of the device to hijack the internal network it’s connected to.
Why this matters?
Vulnerable devices such as this can be used to gain access to internal networks. It is important to keep devices up to date with the latest security patches to close any vulnerabilities before they can be exploited. When a vendor releases updates they should be installed as soon as possible, ideally having been tested before updates are applied in your live environment.
Read more here: https://arstechnica.com/information-technology/2020/07/hackers-actively-exploit-high-severity-networking-vulnerabilities/
27% of consumers hit with pandemic-themed phishing scams
Phishing is the top digital fraud scheme worldwide related to the COVID-19 pandemic, according to new research.
Among consumers reporting being targeted with digital COVID-19 schemes globally, 27% said they were hit with pandemic-themed phishing scams.
Identity fraud is a primary way fraudsters leverage stolen consumer data from phishing and other social engineering schemes. It can have long-term impacts for consumers such as the compromise of multiple online accounts and bringing down credit scores, which we anticipate will increase during pandemic reconstruction.
To better understand the impacts of COVID-19 on consumers, 7,384 adults in Canada, Colombia, Hong Kong, South Africa, the U.K., and the U.S. have been surveyed between June 30 and July 6, 2020.
It asked the consumers if they had been targeted by digital COVID-19 fraud and if so, which digital fraud scheme(s) related to COVID-19 were they targeted with. Globally, 32% said they had been targeted by digital fraud related to COVID-19 with the below being the top types of COVID-19 fraud they faced:
Top global online COVID-19 scams targeting consumers:
Why this matters?
Whatever works for criminals they will continue doing. Until consumers, as well as businesses, get better at detecting these scams and get better at spotting phishing emails criminals will carry on using the latest crisis or tragedy to get users to click on malicious emails and open their networks to attackers.
Read more here: https://www.helpnetsecurity.com/2020/07/24/pandemic-themed-phishing-scams/
New Netflix phishing scam uncovered - here’s how to stay safe
Security analysts have uncovered a dangerous and highly convincing new Netflix phishing scam, capable of evading traditional email security software.
The phishing email masquerades as a billing error alert, pressing the victim to update their payment details within 24 hours or have their Netflix subscription voided.
The link provided in the email redirects to a functioning CAPTCHA form, used in legitimate scenarios to distinguish between humans and AI. Although this step adds a layer of friction to the process, it serves to enhance the sense of legitimacy the attacker is attempting to cultivate.
After handing over account credentials, billing address and payment card information, the victim is then redirected to the genuine Netflix home page, unaware their data has been compromised.
Why does this matter?
Phishing campaigns like this cast a wide net and only need a small number of victims to fall for it to turn a profit, and that means these types of scams are not going to go away any time soon. If no one fell for them they would stop. Always question any email that urges you to take action quickly under the guise of some threat.
Read more here: https://www.techradar.com/news/dangerous-new-netflix-phishing-scam-hits-the-scene-heres-what-you-need-to-know
Common, and dangerous, misconceptions around ransomware - Cyber Tip Tuesday video 28 July 2020
Common, and dangerous, misconceptions around ransomware - Cyber Tip Tuesday video 28 July 2020
Cyber Weekly Flash Briefing 24 July 2020: Cyber crime up 23% Over Past Year, Nearly 50% of employees have made a serious security mistake at work, 99.9% of Hacked Microsoft Accounts Don’t Use 2FA
Cyber Weekly Flash Briefing 24 July 2020: Cyber crime up 23% Over Past Year, Nearly 50% of employees have made a serious security mistake at work, 99.9% of Hacked Microsoft Accounts Don’t Use 2FA
Links to articles are for interest and awareness and linking to or reposting external content does not endorse any service or product, likewise we are not responsible for the security of external links.
Cybercrime Jumped 23% Over Past Year, Says ONS
Cybercrime offenses reported by individuals and businesses have risen 23% over the past year, according to the Office for National Statistics (ONS).
The UK government body explained that 26,215 incidents were referred to the National Fraud Intelligence Bureau (NFIB) by Action Fraud in the year ending March 2020.
The year-on-year increase was driven by a large uptick in the two highest-volume “computer misuse” types reported to Action Fraud. “Hacking – social media and email” saw a 55% increase from 12,894 offenses, and “computer viruses/malware” incidents soared by 61% to reach 6745 cases.
The double-digit increase in reported cybercrime came in spite of improvements to “internal case review processes” and an online reporting tool at Action Fraud in October 2018 which meant some offenses previously categorized as computer misuse are now being properly identified as fraud, ONS said.
Why this matters:
Any increase in reported cyber crime is significant, but such a large rise is even more alarming and demonstrates that firms and individuals need to make sure they are treating these threats seriously.
Read more here: https://www.infosecurity-magazine.com/news/cybercrime-jumped-23-over-past-year#disqus_thread
Nearly half of employees have made a serious security mistake at work
Distraction and burnout can lead to serious mistakes when working online
New research from an email security firm has revealed that almost half (43%) of employees in the US and UK have made mistakes at work that have resulted in cyber security repercussions for themselves or their company.
A survey of 2,000 professionals between the ages of 18 and 51 to find out more about why workers make mistakes and how they can be prevented before they end up turning into data breaches.
Of the employees surveyed, a quarter of them confessed to clicking on links in a phishing email at work. The research also found that employees between 31 and 40 years of age were four times more likely than employees over age 51 to click on a phishing email. At the same time, male employees were twice as likely to do so than their female coworkers.
Why does this matter:
Cyber and Information Security is fundamentally a human problem, not an IT problem, and all the IT controls in the world are worth very little if humans bypass them or fail to follow safe working practices. Ensure your users, at all levels, are aware of the role they play in securing your organisation and make sure they receive adequate and suitable training.
99.9 Percent of Hacked Microsoft Accounts Don’t Use 2FA
Two-factor authentication (2FA) is the single most effective method of preventing unauthorised access to an online account as number from Microsoft prove.
Microsoft tracks over 1 billion active accounts monthly, which is nearly 1/8 of the world’s population. These generate more than 30 billion monthly login events. Every login to a corporate O365 account can generate multiple login entries across multiple apps, as well as additional events for other apps that use O365 for single sign-on.
If that number sounds big, bear in mind that Microsoft stops 300 million fraudulent sign-in attempts every day. Again, that’s not per year or per month, but 300 million per day.
In January 2020, 480,000 Microsoft accounts—0.048 percent of all Microsoft accounts—were compromised by spraying attacks. This is when an attacker runs a common password (like “Spring2020!”) against lists of thousands of accounts, in the hopes that some of those will have used that common password.
Sprays are just one form of attack; hundreds and thousands more were caused by credential stuffing. To perpetuate these, the attacker buys usernames and passwords on the dark web and tries them on other systems.
Then, there’s phishing, which is when an attacker convinces you to log in to a fake website to get your password. These methods are how online accounts are typically “hacked,” in common parlance.
In all, over 1 million Microsoft accounts were breached in January. That’s just over 32,000 compromised accounts per day, which sounds bad until you remember the 300 million fraudulent login attempts stopped per day.
But the most important number of all is that 99.9 percent of all Microsoft account breaches would have been stopped if the accounts had two-factor authentication enabled.
Why this matters:
Two-factor authentication (2FA) is the single most effective method of preventing unauthorised access to online accounts, remediating (or preventing) approximately 95% of attacks. That this simple step, normally available free of charge from online account providers, is so effective means it should be implemented wherever and whenever possible.
Read more here: https://www.howtogeek.com/681419/watch-out-99.9-of-hacked-microsoft-accounts-dont-use-2fa/
Adobe issues emergency fixes for critical vulnerabilities in Photoshop, Bridge, Prelude
Adobe has released an out-of-band emergency security update for Photoshop, Prelude, and Bridge.
On Tuesday, a week after issuing the firm's standard monthly security update, Adobe published security advisories revealing a total of 13 vulnerabilities, 12 of which are deemed critical.
Five vulnerabilities have now been resolved in Photoshop CC 2019 -- versions 20.0.9 and earlier -- and Photoshop 2020 -- versions 21.2 and earlier -- on Windows machines.
All of these vulnerabilities are considered critical, as if exploited, can lead to arbitrary code execution.
Why does this matter:
Vulnerabilities in software are exploited by attackers, patching these vulnerabilities means the vulnerabilities cannot then be exploited. Updates should always be installed as soon as possible to prevent them from being used in attacks.
Read more: https://www.zdnet.com/article/adobe-issues-emergency-fixes-for-vulnerabilities-in-photoshop-prelude/
Blackbaud Hack: Universities lose data to ransomware attack
At least 10 universities in the UK, US and Canada have had data stolen about students and/or alumni after hackers attacked a cloud computing provider.
Human Rights Watch and the children's mental health charity, Young Minds, have also confirmed they were affected.
The hack targeted Blackbaud, one of the world's largest providers of education administration, fundraising, and financial management software.
The US-based company's systems were hacked in May and it has been criticised for not disclosing this externally until July and for having paid the hackers an undisclosed ransom.
In some cases, the data was limited to that of former students, who had been asked to financially support the establishments they had graduated from. But in others it extended to staff, existing students and other supporters.
The institutions the BBC has confirmed have been affected are:
· University of York
· Oxford Brookes University
· Loughborough University
· University of Leeds
· University of London
· University of Reading
· University College, Oxford
· Ambrose University in Alberta, Canada
· Human Rights Watch
· Young Minds
· Rhode Island School of Design in the US
· University of Exeter
In some cases, the stolen data included phone numbers, donation history and events attended. Credit card and other payment details do not appear to have been exposed.
Why does this matter:
Every entity, business, organisation and individual is at risk from ransomware, the bigger the organisation the more point of entries exist but this does not mean this is not a major threat to smaller businesses too. Nearly all these attacks stem from a user clicking on a link in a phishing email so make sure your staff are adept at spotting phishing emails.
Amazon Prime phishing scam returns - here's all you need to know
Shoppers warned of phone and email attacks against Amazon Prime users
Shoppers using Amazon Prime have been warned about a major phishing scam which appears to have resurfaced across the country
The scammers target victims via an automated telephone call claiming that they have opened an Amazon Prime account and that they should "press one" to cancel the transaction.
Doing so will connect the call to a fraudster posing as an Amazon customer service representative who then informs the recipient of the call that their subscription was purchased fraudulently due to a supposed "security flaw" on the targeted person's computer. The bogus Amazon representative then asks for remote access to the recipient's computer, supposedly to fix the security breach. Remote access gives control access allowing the scammers to steal personal information, including passwords and banking information.
There is also an email version of the same scam.
The email version of this scam sees the victim receiving a message stating they have started an Amazon Music subscription charged at £28.99 per month. The email then asks the recipient to click a link if they want to cancel the subscription and receive a refund - but the page they are taken to in order to input their card details and receive the refund will instead send their details to fraudsters.
Why does this matter:
Scammers only need a small number of people they target to fall for the scam for it to be profitable for them, so unfortunately these types of scams are not going to go away any time soon. Make sure you keep up to date with the latest and emerging scams and make sure relatives who might fall victim to these scams are also aware that these types of attacks are happening all the time so to exercise caution if they receive calls or emails of this nature.
Read more here: https://www.techradar.com/uk/news/amazon-prime-phishing-scam-returns-heres-all-you-need-to-know
Phishing attacks concealed in Google Cloud Services
Cyber criminals are increasingly concealing phishing efforts behind legitimate resources.
A lie is best concealed between two truths, an old saying goes, and it seems hackers are using this wisdom to better hide their phishing efforts.
Cyber security researchers are warning of a phishing campaign that utilises Google Cloud Services and offers legitimate PDF whitepapers to victims that give away their login credentials.
According to the researchers, it all starts with a PDF document uploaded to Google Drive, containing a link to a phishing page. The landing page requires the user to log in with their Office 365 or organisation email.
After the victim gives away their login credentials, they are redirected to a genuine PDF report published by a “renowned global consulting firm.”
Why does this matter:
Since the phishing page is hosted on Google Cloud Storage, the user might not become suspicious. Hackers are swarming around the cloud storage services that we rely on and trust, making it much tougher to identify actual phishing attacks. Traditional red flags of a phishing attack, such as look-alike domains or websites without certificates, won’t help us much as we enter a potential cyber pandemic. Users of Google Cloud Platform, even AWS and Azure users, should all beware of this fast-growing trend and learn how to protect themselves. It starts by thinking twice about the files you receive from senders.
Read more here: https://www.itproportal.com/news/phishing-attacks-concealed-in-google-cloud-services/
Analysts Detect New Banking Malware
A new strain of banking malware dubbed BlackRock has been detected by researchers
An investigation into its origins has revealed BlackRock to be derived from the Xerxes banking malware. Xerxes was in turn spawned out of the LokiBot Android banking Trojan, first detected around four years ago.
The source code of the Xerxes malware was made public by its author around May 2019, making it possible for any threat actor to get their hands on it. Despite the code's availability, researchers found that the only Android banking Trojan based on Xerxes' source code that is currently operating appears to be BlackRock.
Why this matters:
This malevolent malware steals credentials not only from banking apps but also from other apps designed to facilitate communication, shopping and business. In total, the researchers found 337 Android apps were impacted, including dating, social networking and cryptocurrency apps.
Read more here: https://www.infosecurity-magazine.com/news/analysts-detect-new-banking/#disqus_thread
Hackers wipe out more than 1,000 databases, leaving only the word 'meow'
Over 1000 unsecured databases have been permanently deleted, leaving only the word “meow” behind.
The attack saw a database that had details of the UFO VPN. UFO VPN, and other products from seemingly the same company, had recently been in the news for exposing user information.
Information exposed include unencrypted account passwords, location information, and IP addresses of user devices and VPN servers.
The VPN, and others like it, claimed that it was not logging user details. Reports alleged that this was not the case.
The attack seems to have come from a bot, according to Forbes, as the attack script overwrites database indexes with random numerical strings and the word ‘Meow’.
Why does this matter:
Unsecured databases are wide open to attackers and not only can the contents be read and information gleaned used in other attacks they can also, as was the case in this attack, be deleted, losing all data.
Is your smart home hosting malware attacks?
It’s not only computers that can be compromised by hackers, almost any electronic device can be compromised – including your smart home gadgets.
Researchers have discovered a new family of malware called Mozi that has been quickly spreading online since last year and appears to have been designed specifically to attack low-power smart devices. Once installed, the malware tries to make contact with other infected devices, adding itself to a botnet (a collection of other compromised devices).
Infected device continues to operate normally however the devices constantly ‘listening’ for instructions from the botnet. The botnet has been designed to launch Distributed Denial of Service attacks (DDoS) that can be used to attack and crash online services and websites. Once activated, your infected devices will be used by hackers to participate in large DDoS attacks.
Some variants can also steal data, or execute additional code, allowing hackers to gain control of your network.
As the malware evolves, the list of affected devices will undoubtedly grow.
Why does this matter:
Almost any electronic device can be compromised to serve malware, be co-opted into taking part in distributed denial of service attacks or otherwise be exploited or used as a point of entry into a network. As more and more of these devices appear in our homes and offices many people do not realise they are significantly increasing their potential attack surface.
Read more: https://www.pandasecurity.com/mediacenter/mobile-news/smart-home-hosting-malware/
Russian cyber attacks an 'urgent threat' to national security
Russia's cyber attack capabilities -- and its willingness to use them -- pose an "immediate and urgent threat" to the UK's national security, according to a report from a committee of MPs.
The long- delayed Russia report from the UK parliament's Intelligence and Security Committee (ISC) describes how it sees Russia's abilities to use malicious cyber activities to further its aims.
"Russia's cyber capability, when combined with its willingness to deploy it in a malicious capacity, is a matter of grave concern, and poses an immediate and urgent threat to our national security," the report said.
Why does this matter:
Given the immediate threat that Russia poses to UK national security, it is concerning that there is no clear coordination of the numerous organisations across the UK intelligence community working on this issue. The risks posed by Russia, and other nation states such as China, Iran and North Korea should not be understated or ignored.
Read more here: https://www.zdnet.com/article/russian-cyberattacks-an-urgent-threat-to-national-security/